{{currentView.title}}
July 12, 2010
How al Qaeda Prepares Attacks against the West: What the July 7-8 Rollup Revealed
KEY POINTS
-
Individuals behind the Times Square attack, New York City subway plot, and the Manchester mall plot all received some level of coordination and support from al Qaeda-linked leaders while they were on the ground in targeted areas.
-
We should not expect al Qaeda-linked attacks against the West to occur independently of one another. Instead, the network of violent Islamist movements led by al Qaeda produces and manages attacks against the West through a three-phase terror attack assembly line: recruiting, pre-deployment and training, and coordination with deployed operatives prior to attacks.
-
Operatives with experience in the Western world have played an increasingly important role in this attack assembly line.
-
Counter-terrorism measures such as drone strikes, financial intelligence, communications intercepts, and other homeland security measures are essential to disrupting al Qaeda and associated movements. But only a strategy that denies control of safe havens to al Qaeda - upon which the network relies for its crucial middle, pre-deployment phase - can succeed in fully rolling back the network.
On July 7 and 8, authorities in the U.S., U.K., Norway, and Germany took action against al Qaeda-linked individuals who had conspired to attack a mall in Manchester, England, the subway system in New York City, and other potential targets. [1] Details brought to light by this multinational rollup and Times Square bomber Faisal Shahzad’s recent guilty plea display close coordination between terrorists in the West and the leadership of al Qaeda and associated movements. Many Islamist terrorists who attempt to strike the West are not simply isolated extremists who become radicalized and choose to carry out an attack independently. Instead, a terror attack assembly line manages would-be terrorists from the time they are recruited until days before they execute an attack. Al Qaeda and its affiliates, such as the Pakistani Taliban, could not operate this assembly line without the use of safe havens abroad.
In the Times Square attack, coordinators from the al Qaeda-affiliated Pakistani Taliban fulfilled the Time Square bomber’s requests for additional funding through two payments sent from Pakistan to the U.S. in March and April 2010.[2] In the New York City subway and Manchester mall plots, an al Qaeda coordinator known as “Ahmad” exchanged emails with the plotters regarding ingredients and selection of explosives. The subway and mall plotters even used a common code in communications with “Ahmad”: subway plotter Najibullah Zazi emailed that the “marriage is ready” before he left Colorado to conduct the attack in New York City in September 2009, and mall plotter Abid Naseer wrote “Ahmad” that he was planning a “wedding” for April 2009.[3]
“Ahmad” served as an intermediary between the plotters and al Qaeda leaders, including Saleh al Somali, an individual who served as part of an al Qaeda “external operations” branch charged with overseeing attacks upon the West. Somali, for example, helped recruit Zazi and other members of the cell plotting to attack the New York City subway.[4] Two other individuals reportedly served alongside Somali: Rashid Rauf, who designed the 2006 plot to bring down airliners traveling to the U.S. from Britain, [5] and Adnan el Shukrijumah, whom authorities charged in the July 7-8 rollup.[6] U.S. drone strikes killed both Rauf and Somali in the last two years, leaving Shukrijumah as the sole surviving leader of the external operations branch.[7] Shukrijumah’s experience makes him an increasingly important asset for al Qaeda, as less-experienced operatives and intermediaries have likely filled the gaps left by Rauf and Somali.
The FBI first began searching for Shukrijumah, who has a $5 million bounty on his head, in March 2003, when Khalid Sheikh Mohammad identified his photograph. Shukrijumah would soon help fill the vacuum Mohammad’s capture left in al Qaeda by playing a key role in training and operations.[8] He had a part, for example, in plans to blow up John F. Kennedy airport and U.S. apartment buildings, had ties to “dirty bomber” Jose Padilla, and may have been associated with hijacker Mohammed Atta prior to 9/11.[9]
Evidence from the subway and Manchester plots reveals that al Qaeda coordinators play a guiding role in preparing attacks against the West as part of what appears to be the third phase of an al Qaeda terror attack assembly line. First, al Qaeda and its affiliates try to recruit English-speaking individuals with visas, residency permits, or citizenship in Western countries. This entails encouraging extremism among targeted recruits and providing individuals who have already become radicalized with the tools to act upon their militant beliefs. Second, the network trains and deploys potential recruits in safe havens around the world. Third, the network coordinates, supports, and directs operations while the recently trained al Qaeda-linked operatives are on the ground in targeted countries.
This may not apply to all cases of Islamist terrorism. Nidal Hasan, for example, despite expressing grievances common to Islamist terrorists and communicating with al Qaeda-linked cleric Anwar al Awlaki, does not appear to have received direct coordination for the assault he launched upon soldiers at Fort Hood. These three phases do provide, however, a rough rubric to help one understand how the al Qaeda network appears to launch most attacks against the West.
The implementation of the program’s first phase can be seen in the al Qaeda network’s use of foreigners with experience in the Western world to conduct attacks and in the large numbers of Westerners who have traveled to fight alongside terror groups in countries such as Yemen, Somalia, and Pakistan. Al Shabaab increasingly relies upon foreign fighters from America, such as Abu Mansour al Amriki, who has risen to prominence as a spokesman in the group’s propaganda videos and as a regional military commander for the group.[10] As recently as June 8, two New Jersey men attempted to travel to Somalia to join al Shabaab.[11] More than two dozen other Somali-Americans may have left communities in Minneapolis to train in Somalia, and the FBI fears some may have returned to the U.S. to carry out operations.[12] Shukrijumah’s rise to power, as an English-speaking individual with an ease for technology, shows how the al Qaeda network has structured its personnel to enhance its contact with Westerners.
Christmas Day Bomber Umar Farouk Abdulmutallab and Times Square bomber Faisal Shahzad also traveled to al Qaeda safe havens (Yemen and Pakistan, respectively) prior to their operations, demonstrating the importance of the second, pre-deployment phase. Such a phase could not occur without territory held by al Qaeda and its affiliates in several countries across the world, physical space that also allows al Qaeda to shelter key leaders, conduct planning, and weaken regional allies of the West.
Shukrijumah’s long resume and the revelation of an al Qaeda external operations branch means we should not expect terror attacks against the West to occur independently of each other. Terror plots and attacks exist within a complex, larger framework designed by the next generation of al Qaeda leadership. While this should increase concern – it provides evidence that the terrorist groups methodically plans attacks against Western interests on Western soil – there is a silver lining.
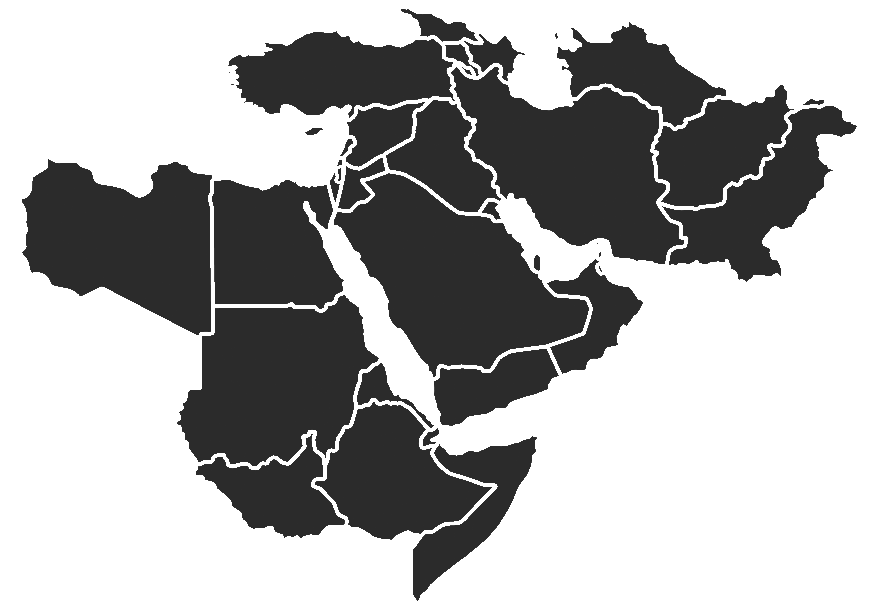
The West can defeat an operational network much more easily than a series of random attacks launched by self-radicalized individuals without connections to larger organizations. The use of counter-terrorism tactics, including drone strikes, financial intelligence, communications intercepts, and other enhanced homeland security measures, are essential to disrupting al Qaeda’s activities. But without a strategy to reduce the control al Qaeda and its affiliates maintain over safe havens in the Middle East, South Asia, and Africa, al Qaeda will still be able to achieve the critical middle step of its attack assembly line and sustain its command-and-control. Defeating al Qaeda’s external operations branch and reducing the likelihood of further attacks upon the West demands a strategy that will uproot the base of the al Qaeda and associated movements network.